|
Every year I donate money to the Wikimedia foundation. If the organisation sounds familiar but you are not sure why it's because you most likely use one of their biggest contributions to the world - Wikipedia.
Every week, some weeks multiple times, I reference and learn from the wealth of information that can be found within Wikipedia. This information is of course contributed by volunteers (essentially) who don't receive payment for their writings and then potentially re-edited by others who have a differing view, opinion or understanding of the topic. It's the openly editeditable nature that leads some to mark Wikipedia as an unreliable source of information. That's fine, I use it all the time and learn a heck of a lot. One website will never be my only source of learning so I build my own resilience to misinformation - at least as good as the common man - and thus I personally vouch for the overall richness of Wikipedia, at least for the topics that interest me. I give $10. I feel a small amount of good through making a donation to a non-profit organisation that directly benefits me. Critically important to assisting the good feeling is making the process to give simple, hoopless and fast. The Wikiemedia Foundation has not gone the path of many charities where they require direct debit capability and an ongoing commitment with monthly "subscription" style payments (a practice of which I can appreciate the benefits - but frankly it turns me off). With a simple website I am able to select a $10 donation amount. Other options are available, including a subscription, and it is possible to manually enter an amount also. The modes of payment are simply PayPal or Credit Card/Debit or BPay and the transaction is no fuss and requires as few clicks as are necessary. They have done it right. I do get very polite emails once an a while from Jimmy Wales, the Wikipedia Founder, asking simply for another donation. He keeps it short and to the point and is clearly grateful. I find the entire thing admirable... maybe it helps that I am a beneficiary in that I can use the site... I won't self-analyse too deeply. So, the donation goes towards (as copied from the payment site): Technology: Servers, bandwidth, maintenance, development. Wikipedia is one of the top 10 websites in the world, and it runs on a fraction of what other top websites spend. People and Projects: The other top websites have thousands of employees. We have about 300 staff to support a wide variety of projects, making your donation a great investment in a highly-efficient not-for-profit organization. Cool! So I know how much I'm paying... I know who I'm paying and most importantly I know what they use the money for. I use Wikipedia a lot. Sometimes I find myself surprised that I'm reading a Wikipedia page. It's because there is a distinct lack of adverts and bulky noise that make up the rest of the Internet. There is little to take your attention away from the stuff that matters. You might find this too. I suspect if you're in a technical field and you look to the Internet for quick info you'll find Wikipedia is a common source for you as well. Maybe it's time to help them out? Just a little bit... Thanks Wikimedia Foundation, Thanks Jimmy and thanks to all the Wikipedia contributors.
Comments
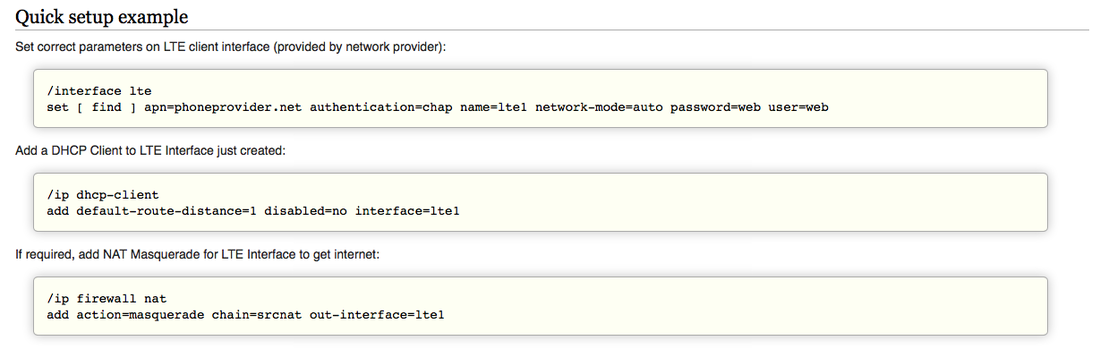
 If you need a remotely accessable field deployable network it’s helpful to work with a recipe. There are a lot of ways to do this and some really nifty and cheap ways at that. But from what I can see a lot of reading of forums and multi-lingual Youtube videos may be required… that won’t do. NOTE: This is a work in progress… so far the solution is not perfect and will be updated as I learn more. I needed a smart, flexible solution for remote access to field deployed tools - and with little time to research I looked towards a solution I was fairly confident would work. MikroTik create routers of all shapes and sizes, from small routers that would fit inside roadside comms pits to rack mountable, multi-core enterprise ready routers that cost a fraction of what you might expect. The software operating system (called RouterOS) is widely supported both by MikroTik and a huge worldwide user base and people put it through it’s paces in all sorts of scenarios. My particular need is 3G or 4G remote access, potentially some dynamic DNS to pretty up the remote access and make the dynamic IP assignment of the 4G network less bothersome, and some firewalling for just in case. MikroTik tiks (sic) all those boxes. The 4G dongle/chip piece is a challenge, however. So far the Optus 4G USB dongle isn’t activating smoothly and I suspect it needs a firmware flash to allow the public IP address to be passed through to the MikroTik rather than running internal NAT. MikroTik has a list of supported LTE cards and modems here: http://wiki.mikrotik.com/wiki/Supported_Hardware#4G_LTE_cards_and_modems The Optus 4G dongle is a variant of the Huawei E3372h - and was cheap at the supermarket (50% off on sale), so potentially bricking it via firmware update is no issue. To date I have the MikroTik dishing out private IP addresses to clients (wired or wireless) which can then route out through the 4G dongle using NAT. Once the Optus SIM activation is complete this should result in web access, at this stage the activation page is acting as a captive portal to all client traffic.
So far this recipe doesn’t allow for remote access using dynamic DNS as there is effectively a double NAT in the way and no firewall rules allowing any traffic through from the public side. It looks like flashing the USB dongle is definitely required as there is no security pass-through settings in the E3372 web interface like some report seeing.
Have you done this? Comment below if you have any tips or tricks. It's time to upgrade your Apple mobile devices. Quickly, go and do it now and come back to read why afterwards. If you are not running Apple iOS 9.3.5 or later on your iPhone, iPod or iPad you should want to add an upgrade to your to do list in the very near future. Apple work very hard to build security in to their mobile operating system. That's why when the Cupertino giant released iOS 9.3.5 in August 2016 to fix not one but three zero-day vulnerabilities the tech-news feeds went haywire. If you missed it let us know in the comments below. iOS 9.3.5 was released only a matter of weeks after 9.3.4 as Apple's security team worked quickly to plug the holes which were found in the wild only 10 days before thanks to the quick thinking of a likely target of the exploits from the United Arab Emirates. The security vulnerability researchers involved (from Citizen Lab and Lookout) suspect the vulnerabilities may have been known to the initial finders as far back as iOS 7 (2013). Citizen Lab have called out Israeli company NSO Group as the developers of Pegasus which is thought to be the name of the software within which the exploits can be launched. While it may seem unlikely that you would become a target of such an underground and probably extraordinarily expensive hacking tool, unless you have ties to government, extreme wealth or a multinational company with high value intellectual property, now that the vulnerabilities have been announced they are more likely to be researched widely by a larger security research base, including organisations who profit from crime. The fact is that these are zero-day vulnerabilities which by definition were unknown (other than by presumably the NSO Group, and their clients) and un-patched until now. In the case of the UAE target the story goes that social engineering or phishing attempt was made through a message to his or her mobile phone. The unknown sender left the recipient suspicious so they passed it on to Citizen Lab to investigate. Had they unwittingly followed the link they would have opened a pathway to all the data and communication from their phone to be viewed by an unknown party. This includes communciation from applications such as WeChat, Facebook Messenger, Skype, WhatsApp, Viber, Gmail, Apple's iMessage and more. The rest is history, yet we now live in a world where this is the future. Cyber crime and espionage is the new norm - with governments and criminals playing the same game. Of course money and power are at the centre of it all... In 2015 a privately held cyber-security research company Zerodium offered to pay $1 million for information about a Zero Day Bug in Apple's iOS 9. The reason Zerodium is forking out so much for information on these bugs is because it then on-sells that information, including "protective measures and security recommendations, to its clients". The clients are touted as Government and Corporate, yet only a "limited number of organisations" will have access to the solutions and capabilities - which likely drives up the price due to exclusivity. So, it's time to patch your devices and stay alert. If you manage a network or part of a networks infrastructure may this also be a timely reminder to check through your security best practices and policies, change default settings and always read the release notes of the software upgrades and fixes for your hardware.
Have you updated yet? I was fortunate enough to have some alone time with NetScout’s brand new AirCheck G2 (announced May 17, 2016). I tried to play with every feature and capture every screen but there are just so many tricks in this handy box… Here is what I liked.
The AirCheck G2 is green, very green! I find it difficult to identify how I actually feel about the old yellow or the new green. The colour does provide a critical function as hand held tools are easy to put down and leave somewhere. Bright colours aid finding and reminding not to leave the unit behind. This is a tool for people tasked with any variation of the following roles: managing, maintaining, installing, securing, troubleshooting, testing, hacking, supporting and auditing wireless networks. Within 10 seconds of being turned on the AirCheck begins to scan the nearby wireless environment. It collects information about networks, Access Points, clients and channels which are all accessible under corresponding menu buttons on the home screen. You can tell your AirCheck is working hard in the background as it indicates the current channel being scanned at the top of the screen. It’s also likely the counters indicating found networks, Access Points and clients are increasing on each button.
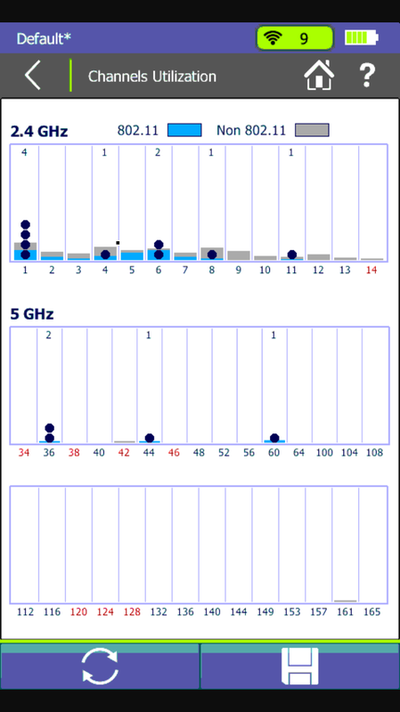
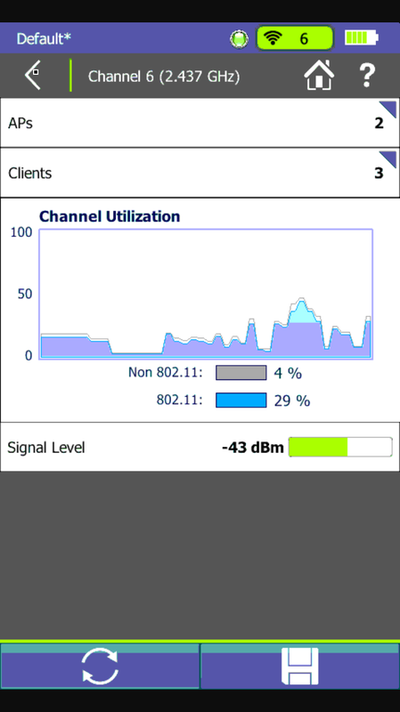
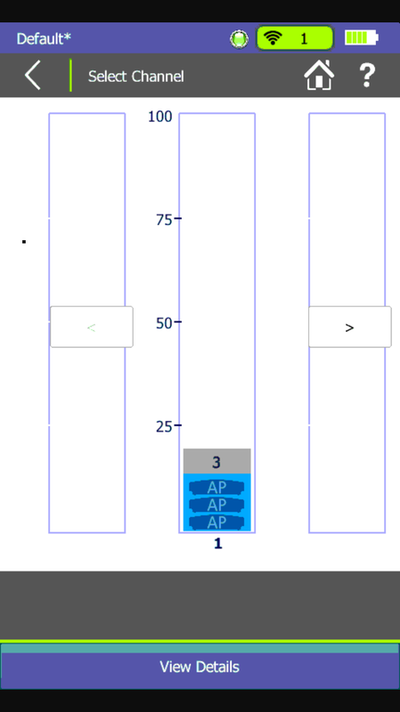
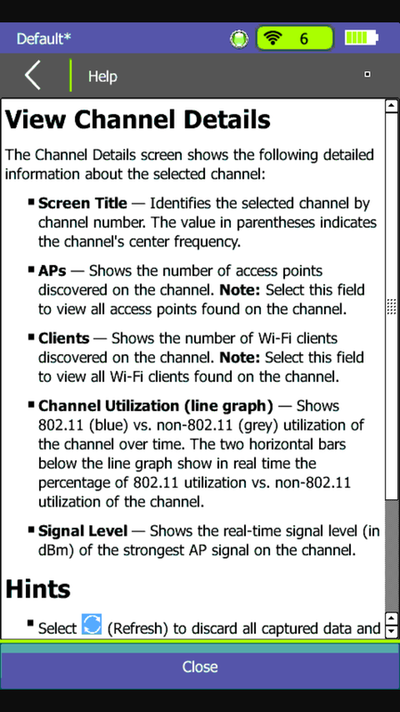
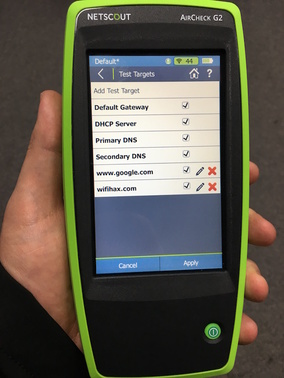
The channel utilisation screen is much like the previous AirCheck with a bar for each channel in which dots report Access Points detected, blue bars report channel utilisation caused by 802.11 sources and grey bars represent non WiFi utilisation. This is a great screen for a rapid view of the WiFi environment. Note though that this is not a spectrum analyser. Selecting a channel from here presents a more granular look at utilisation, signal level in dBm and direct access to view the clients and Access Points which are operating on the channel.  Hunting down specific Access Points or clients is made easier with the Locate feature, which is an option if you select a specific station from either the Access Points or Clients lists. I liken an AirCheck in this mode to a security guards handheld metal detector for WiFi Engineers. You’ll hear beeps increasing in frequency as you near your target (this can be muted if you are hoping for a silent kill) and the signal strength indicator and histogram assist in human computed trilateration. If client or crowd density, time to find or large distances are factors in your search then the exorbitant directional antenna option would be handy. This allows the operator to better isolate the direction in which signal from the station is at its strongest. Simply seeing whats nearby is cool but testing the network is where the AirCheck G2 begins to pay for itself. With the ability to associate to WPA2 Enterprise network (and all lesser options) with a great variety of EAP options the AirCheck can squash the time required to audit and test connecting to wireless networks. This is a good idea after deploying new infrastructure. You can even pre-load network profiles via the management software available for 64-bit Windows 7, 8 and 10 devices. Once connected you can perform roaming tests with detailed logging and check connectivity to DHCP, gateway, websites and DNS. Some of this data is then uploaded to Link-Live (for cloud logging) or full session data can be exported to the Windows management application.
Curiously, the right hand side of the AirCheck G2 is home to three USB ports. On that note I will finish up with one word: Roadmap Loves:
I would Love:
If you are not already standing and shouting at your computer “Shut up and take my money” let me know why in the comments below. If you are interested in buying one (Australia/NZ and Asia Pacific readers) then let me know here.
Links: AirCheck G2 - Virtual Test Drive & Product Specs AirCheck G2 - Overview Video WifiHax at CWNP - Dilip Advani demonstrates the AirCheck G2 live
I went hunting for a slide deck I'd presented on Wi-Fi security a couple of years ago and instead found this update I put together for a mini road-show in late 2015 for K12 IT Teams.
These slides were accompanied by loads of talking and I remember spending a lot of time drawing on the whiteboard. |
WifiHaxWe build and optimise networks. Continuous learning is our secret to being good. Along the learning journey we will share things here... Archives
May 2024
Categories
All
|







 RSS Feed
RSS Feed