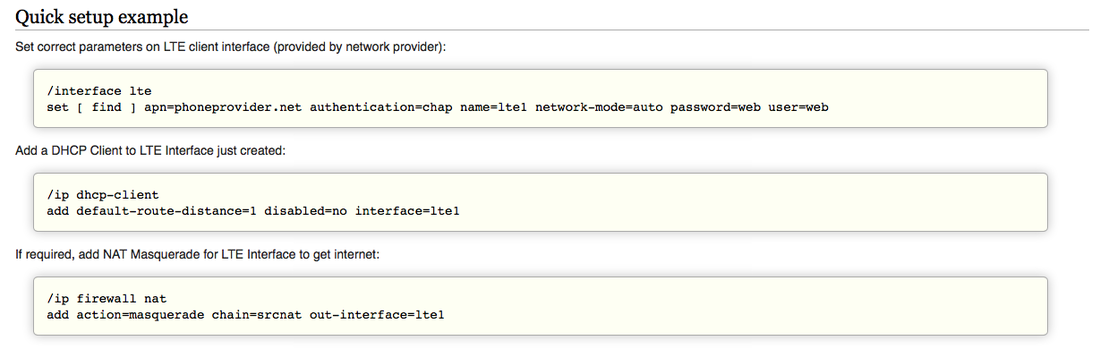
 If you need a remotely accessable field deployable network it’s helpful to work with a recipe. There are a lot of ways to do this and some really nifty and cheap ways at that. But from what I can see a lot of reading of forums and multi-lingual Youtube videos may be required… that won’t do. NOTE: This is a work in progress… so far the solution is not perfect and will be updated as I learn more. I needed a smart, flexible solution for remote access to field deployed tools - and with little time to research I looked towards a solution I was fairly confident would work. MikroTik create routers of all shapes and sizes, from small routers that would fit inside roadside comms pits to rack mountable, multi-core enterprise ready routers that cost a fraction of what you might expect. The software operating system (called RouterOS) is widely supported both by MikroTik and a huge worldwide user base and people put it through it’s paces in all sorts of scenarios. My particular need is 3G or 4G remote access, potentially some dynamic DNS to pretty up the remote access and make the dynamic IP assignment of the 4G network less bothersome, and some firewalling for just in case. MikroTik tiks (sic) all those boxes. The 4G dongle/chip piece is a challenge, however. So far the Optus 4G USB dongle isn’t activating smoothly and I suspect it needs a firmware flash to allow the public IP address to be passed through to the MikroTik rather than running internal NAT. MikroTik has a list of supported LTE cards and modems here: http://wiki.mikrotik.com/wiki/Supported_Hardware#4G_LTE_cards_and_modems The Optus 4G dongle is a variant of the Huawei E3372h - and was cheap at the supermarket (50% off on sale), so potentially bricking it via firmware update is no issue. To date I have the MikroTik dishing out private IP addresses to clients (wired or wireless) which can then route out through the 4G dongle using NAT. Once the Optus SIM activation is complete this should result in web access, at this stage the activation page is acting as a captive portal to all client traffic.
So far this recipe doesn’t allow for remote access using dynamic DNS as there is effectively a double NAT in the way and no firewall rules allowing any traffic through from the public side. It looks like flashing the USB dongle is definitely required as there is no security pass-through settings in the E3372 web interface like some report seeing.
Have you done this? Comment below if you have any tips or tricks.
Comments
|
WifiHaxWe build and optimise networks. Continuous learning is our secret to being good. Along the learning journey we will share things here... Archives
May 2024
Categories
All
|

 RSS Feed
RSS Feed